## How 500ms Saved the Internet: The XZ Backdoor
This is not a “hackers broke Linux” post.
This is not fear-mongering.
This is the actual anatomy of a near-catastrophic supply chain attack.
No zero-days.
No buffer overflows.
No flashy exploit chains.
Just patience, psychology, and one 500ms delay that felt off.
That was enough.
### Table of Contents
- Why XZ Utils Matters More Than You Think
- The Long Con: Infiltrating an Open-Source Project
- Where the Backdoor Actually Lived
- Build-Time Code Injection Explained
- How the XZ Backdoor Hooked Into SSH
- Why Traditional Security Tools Failed
- The 500ms Delay That Triggered Everything
- Why This Almost Went Global
- What the XZ Backdoor Changed Forever
- Final Thoughts
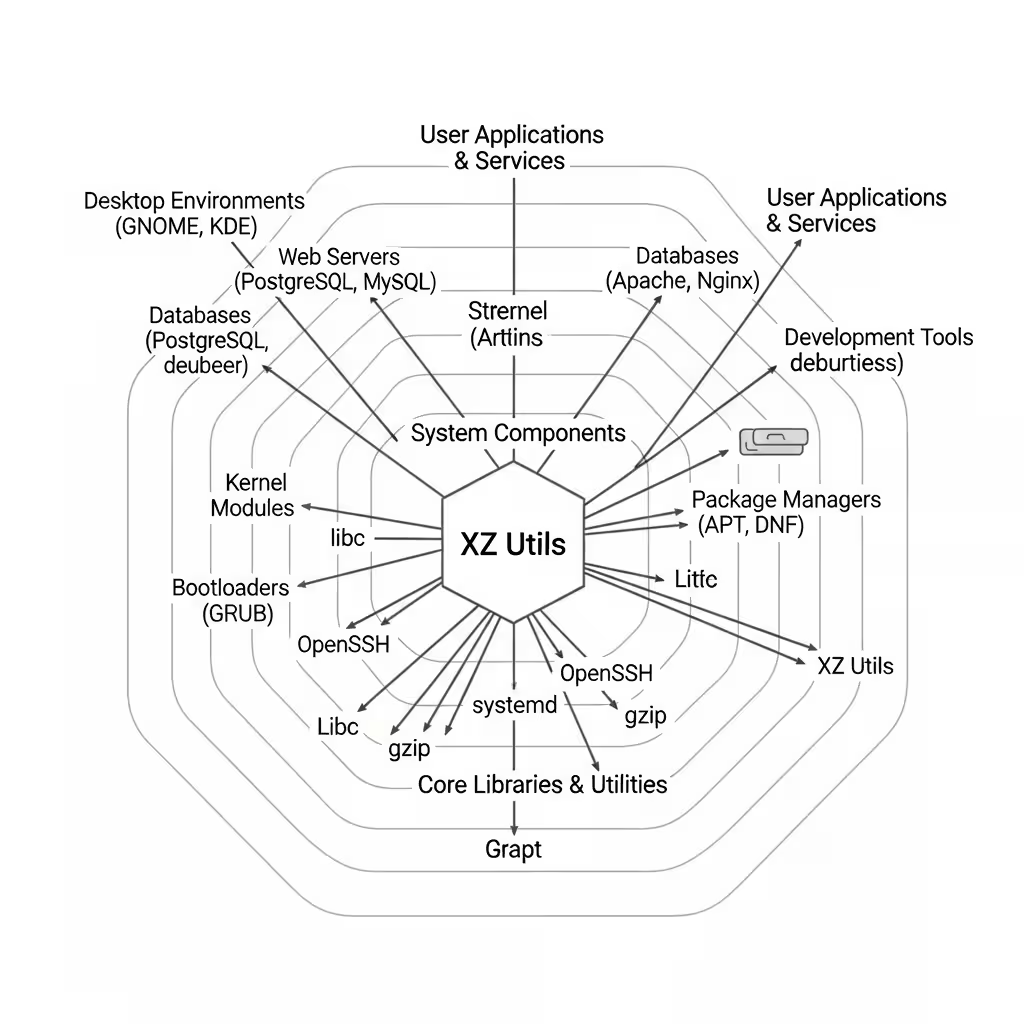
### Why XZ Utils Matters More Than You Think
XZ Utils is boring.
That’s the point.
It’s a compression library — specifically liblzma.
It doesn’t open windows.
It doesn’t talk to users.
It just sits there… quietly used by:
- Linux distributions
- Package managers
- System services
- SSH-related tooling
- Build pipelines
You don’t run XZ.
Everything else runs it.
Which makes the XZ backdoor terrifying.
This wasn’t an attack on an application.
It was an attack on assumptions.
### The Long Con: Infiltrating an Open-Source Project
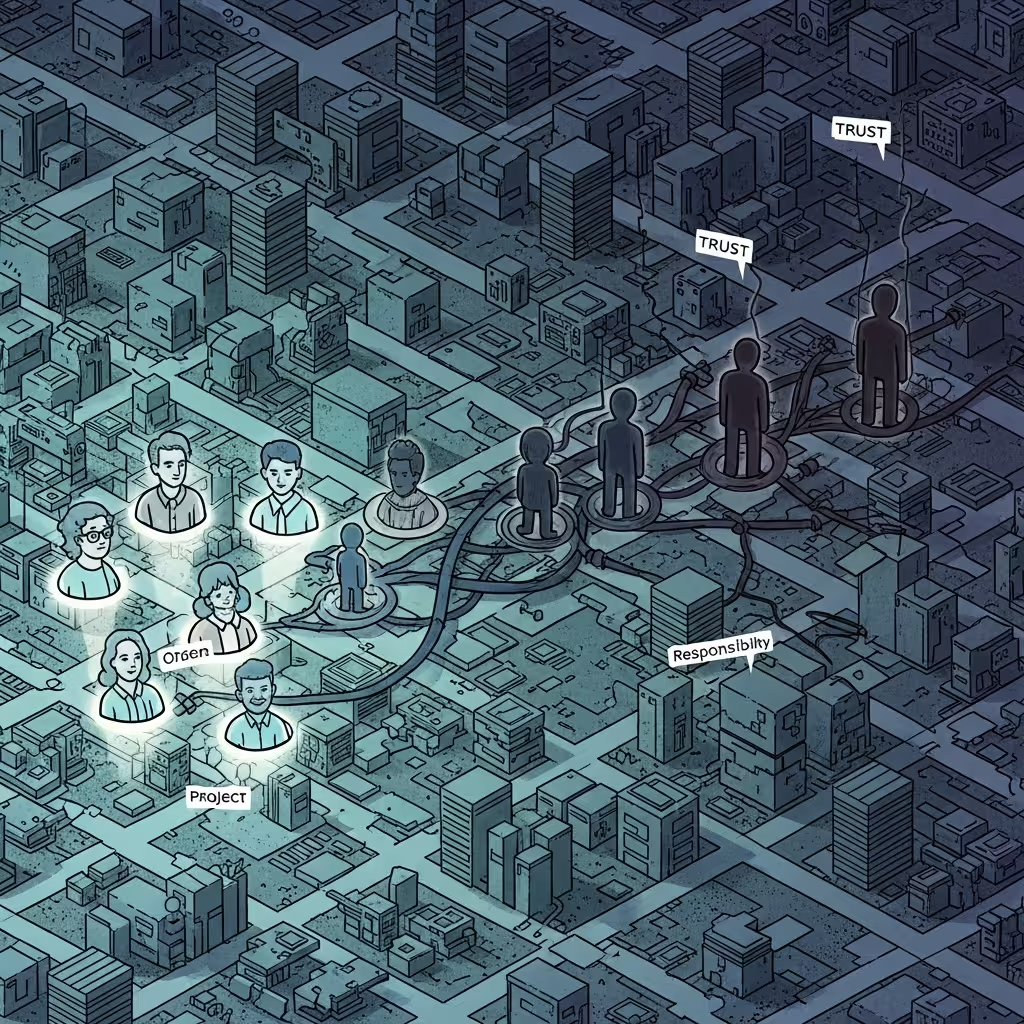
The attacker didn’t start with malware.
They started with emails.
Over multiple years:
- Bug fixes
- Helpful patches
- Pressure on the exhausted maintainer
- Consistent, calm participation
Eventually, a new contributor emerged as indispensable: Jia Tan.
This wasn’t hacking.
This was social engineering at maintainer scale.
Open source has a dirty secret:
Projects don’t fail technically.
They fail when maintainers burn out.
And that’s exactly what happened.
### Where the Backdoor Actually Lived
Here’s where things get clever — and scary.
The XZ backdoor was not a clean chunk of malicious code sitting in a .c file.
Instead, it was:
- Split across files
- Obfuscated
- Activated conditionally
- Injected during the build process
Meaning:
- Reading the source? Looks fine.
- Skimming diffs? Looks boring.
- Running tests? Nothing breaks.
This is modern supply chain warfare.
### Build-Time Code Injection Explained
Most developers trust build systems blindly.
That’s the mistake.
In this case:
- The malicious logic lived in test-related files and build scripts
- During compilation, crafted macros and objects were stitched together
- The final binary contained behavior not obvious from source
Conceptually, it looks like this:
Source Code → Build System → Binary
(clean) (infected) (backdoored)Security reviews focus on source.
The attacker focused on transformation.
That’s the gap.
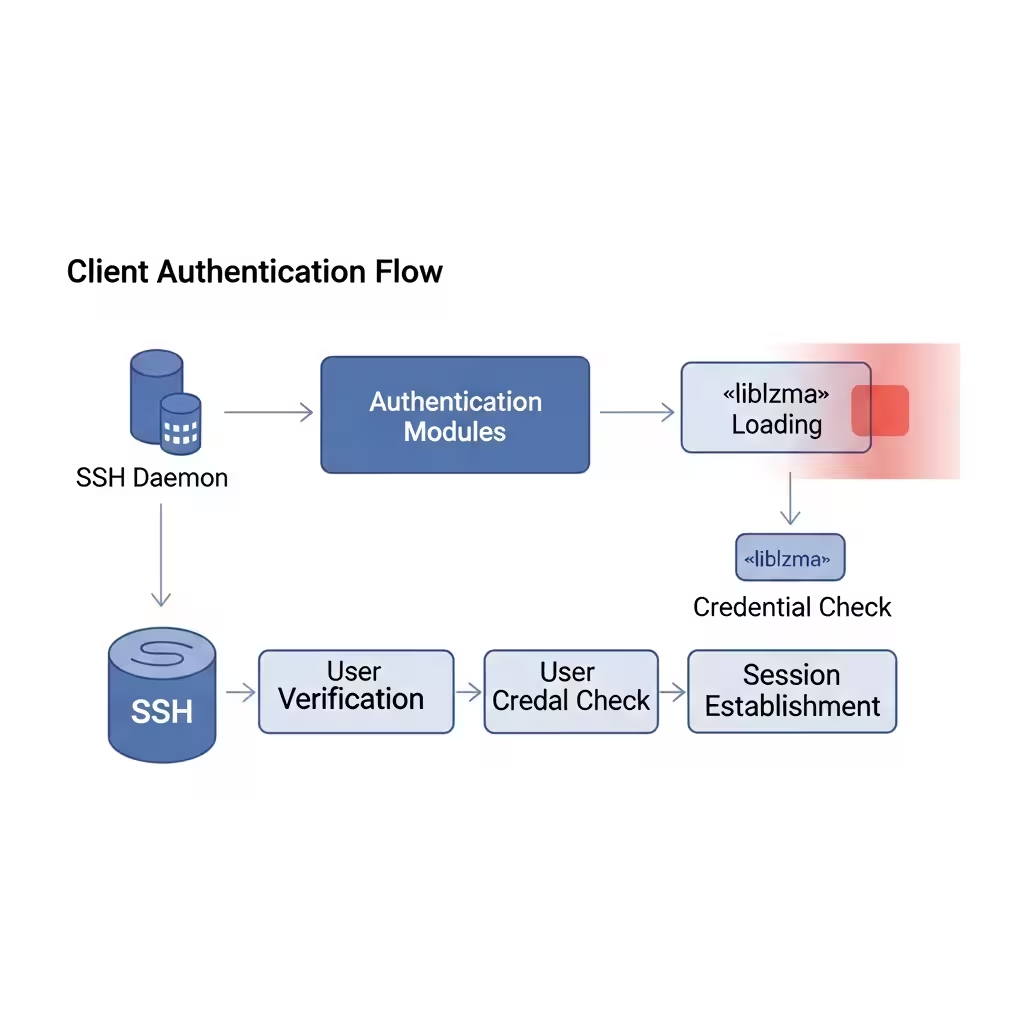
### How the XZ Backdoor Hooked Into SSH
This is the part that almost ended very badly.
The backdoor targeted:
liblzma- Loaded indirectly by OpenSSH
Once loaded, it:
- Interfered with cryptographic routines
- Hooked authentication paths
- Allowed a crafted input to bypass normal SSH checks
No logs.
No crashes.
No warnings.
If you had the right key sequence, you were in.
This wasn’t noisy malware.
It was surgical.
### Why Traditional Security Tools Failed
Let’s be clear: this wasn’t incompetence.
This was out-of-scope for most tools.
Why antivirus failed:
- No known signatures
- No malicious runtime behavior by default
Why static analysis failed:
- Obfuscation
- Distributed logic
- Build-time activation
Why code review failed:
- Legit-looking patches
- Years of trust
- No single “evil commit”
Security tools assume attackers are loud.
This attacker whispered.
### The 500ms Delay That Triggered Everything
A Microsoft engineer noticed something tiny:
SSH logins were slower than usual.
Not broken.
Just… wrong.
That extra ~500 milliseconds led to:
- Profiling CPU usage
- Inspecting binary symbols
- Tracing unexpected behavior
And slowly, painfully, the XZ backdoor unraveled.
No alert system caught it.
A human did.
That detail alone should scare you more than the exploit itself.
### Why This Almost Went Global
Timing saved us.
The backdoored versions:
- Had reached major distributions
- Were close to stable releases
- Had not yet fully propagated
If this slipped a bit longer:
- Cloud infrastructure compromised
- SSH trust broken
- Global incident response chaos
This wasn’t theoretical damage.
This was one release cycle away from disaster.
### What the XZ Backdoor Changed Forever
After this, open source stopped pretending.
Hard truths:
- Trust is a dependency
- Maintainers are single points of failure
- Supply chain attacks scale better than exploits
We didn’t dodge this because we were prepared.
We dodged it because someone felt annoyed.
That should unsettle you.
### Final Thoughts
The XZ backdoor wasn’t stopped by AI.
Or policy.
Or security theater.
It was stopped by curiosity.
By someone refusing to ignore a small anomaly.
Modern security isn’t about paranoia.
It’s about paying attention.
Sometimes, 500ms is all you get.
And this time — it was enough.